Project Risk Management Processes
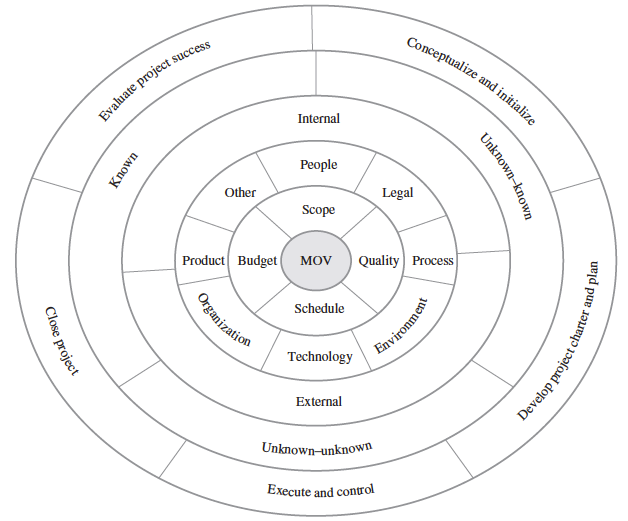
Effective risk management requires a systematic process and a commitment to follow that process by the project’s stakeholder. Figure 1 provides a framework that outlines six steps for managing project risk.
The six steps include:
- Create a Risk Plan
- Requires firm commitment by all stakeholders to the entire Risk Management approach
- Risk Management should align throughout the organization
- Risk Planning focuses on preparation
- Systematic preparation and planning can help minimize adverse effects on the project while taking advantage of opportunities as they arise
- Identify Risks
Risk identification deals with identifying and creating a list of threats and opportunities that may impact the project’s measurable organizational value (MOV) and/or project activities. Each risk and its characteristics should be documented to provide a basis for the overall risk management plan.
- Through Project Risk Identification Framework
Figure 2 Project Risk Management Processes
(Source: Information Technology Project Management – Fifth Edition)
- Through Risk Identification Tools & Techniques
- Learning Cycles
- Brainstorming
- Nominal Group Technique
- Delphi Technique
- Interviews
- Checklists
- SWOT Analysis
- Cause & Effect (a.k.a. Fishbone/Ishikawa)
- Past Projects
- Analyze Risks
Risk assessment focuses on prioritizing risks so that an effective strategy can be formulated for those risks that require a response.
- Qualitative Approaches
- Quantitative Approaches
- Develop Risk Strategies
- Risk strategies depend on:
- The nature of the risk itself – Really an opportunity or threat?
- Impact of the risk on the project’s MOV and objectives – Likelihood? Impact?
- The project’s constraints in terms of scope, schedule, budget, and quality requirements – Successful response possible with available resources?
- Risk tolerances or preferences of the project stakeholders
- Strategies to respond to opportunities with potential positive impacts on the project goal and objectives
- Exploitation – attempt to take advantage of the situation
- Sharing of Ownership – e.g. joint partnerships or joint ventures with customers or vendors
- Acceptance – PM and project team members’ minds are open in order to take advantage of opportunities as they arise
- Strategies to respond to a particular risk in terms of a threat may follow one of the following strategies:
- Accept or Ignore
- Management Reserves
- Released by senior management
- Contingency Reserves
- Part of project’s budget
- Contingency Plans
- Avoidance
- Mitigate
- Reduce the likelihood or impact (or both)
- Transfer
- g. insurance
- Management Reserves
- Monitor and Control Risks
Various tools exist for monitoring and controlling project risk. These include:
- Risk audits – focus on ensuring that the project manager and team have done processes are in place. Should be conducted by people outside the project team.
- Risk review – throughout the project life cycle, the project stakeholders should hold scheduled, periodic risk review. Can be conducted internally.
- Risk status meetings and reports – should provide a formal communication system for monitoring and controlling project risks.
- Respond and Evaluate Risk
Risk response plan that includes:
- A trigger which flags that the risk has occurred
- An owner of the risk (i.e., the person or group responsible for monitoring the risk and ensuring that the appropriate risk response is carried out)
- A response based on one of the four basic risk strategies
- Adequate resources
Source:
Marchewka, J. T., 5th edition. Information Technology Project Management : Providing Measurable Organizational Value. Singapore: John Wiley & Sons, Inc..